Card access control systems have become an essential component of modern security, providing businesses with the ability to monitor and manage access to their facilities at any time, from anywhere in the world. In this article, we will delve into the basics of card access control, including how these systems work, their benefits, and key components like access control card readers and electrified door hardware. We'll explore the world of card access control systems to help you make informed decisions for the security needs of your business, building or facility.
Card Access and Key Fob Access Control Systems: Door Security Systems
 Card access control systems, also known as key fob access control systems, are door security systems that utilize electronic card readers with key fobs to grant or deny access to specific areas within a building or facility. These access control systems offer increased security, improved control over door access, and a more efficient way of managing entry permissions for employees, visitors, and contractors. An access control system or key fob security system will allow you to easily manage access to the door lock devices of your building, whether you are controlling the devices on your phone with mobile access, or utilizing a credential such as a key card or key fob, while physically on the property.
Card access control systems, also known as key fob access control systems, are door security systems that utilize electronic card readers with key fobs to grant or deny access to specific areas within a building or facility. These access control systems offer increased security, improved control over door access, and a more efficient way of managing entry permissions for employees, visitors, and contractors. An access control system or key fob security system will allow you to easily manage access to the door lock devices of your building, whether you are controlling the devices on your phone with mobile access, or utilizing a credential such as a key card or key fob, while physically on the property.Components of Card-Based Access Systems
A typical card-based access system consists of several components. One of the most important is the access control card reader, which reads information from the key card or key fob and determines if access should be granted or denied. Another essential component is the credential, another word for an electronic key. An access credential can be a key card, key fob, or a mobile device, which contains embedded electronic information that can be read by the access control card reader.
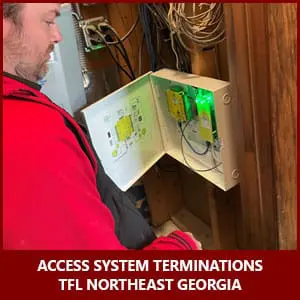 All card access control systems need a brain, not a human brain, but a way to communicate from the card reader and credential to make access decisions at the opening. This comes in the form of a control board or access control panel, which serves as the central hub of the card access system and is responsible for managing card reader access control devices and storing access data.
All card access control systems need a brain, not a human brain, but a way to communicate from the card reader and credential to make access decisions at the opening. This comes in the form of a control board or access control panel, which serves as the central hub of the card access system and is responsible for managing card reader access control devices and storing access data.
Now that there is a way to grant or deny access, how does the door unlock or stay locked? This is where electrified door hardware comes into play. Electronic door locks are required to be integrated into the system, enabling door access control systems to control entry. Finally, access control software is used to manage, monitor, and control the entirety of access systems. This software can be server-based, hosted on a computer on-site, or cloud-based, hosted on a server in the cloud. Many systems these days are transitioning to cloud-based access control software to enable end-users to manage their property from any device, at any time, from anywhere in the world.
What Types of Access Cards & Key Fobs are used in Card Access Control Systems?
Card-based access control security systems use different types of access credentials, including key cards and key fobs. Key cards can be magnetic stripe cards that store access information on a magnetic stripe, RFID cards that communicate with the access control card reader wirelessly, or smart cards with a built-in microprocessor capable of storing and processing data for added security and functionality. Key fobs use RFID technology, similar to RFID cards, but are often more compact and convenient to carry.
 Various types of access credential types exist depending on the level of security needed. Proximity cards, or prox cards for short, were once considered very secure but have since left access systems vulnerable due to the ability to easily duplicate the cards with low-cost hardware that can be purchased online. The ease of being able to duplicate a credential is not something you want to risk when the security of your building and safety of its patrons are on the line.
Various types of access credential types exist depending on the level of security needed. Proximity cards, or prox cards for short, were once considered very secure but have since left access systems vulnerable due to the ability to easily duplicate the cards with low-cost hardware that can be purchased online. The ease of being able to duplicate a credential is not something you want to risk when the security of your building and safety of its patrons are on the line.
However, it doesn’t mean all prox cards are bad, it’s the level on encryption within the credential that matters. Key cards can utilize different encryption and a leading manufacturer, HID, offers the industry’s broadest range of smart card-based credentials such as iClass, iClass SE, Indala, Crescendo, Flexsmart/MIFARE DESFire, MIFARE Classic and Seos, just name a few.
Other types of credential technology has become more common and reliable these days. Biometric readers utilize facial recognition or a thumbprint to determine access so essentially, a person is the access credential. Bluetooth, Near Field Communication (NFC) credentials and smartphones are very convenient for end users as well.
With so many options it can be overwhelming but it’s critical to choose what’s best for your specific needs. Always reach out to a professional security provider like The Flying Locksmiths to review your security requirements and we’ll guide you on the correct access credentials for your application.
Advantages of Card-Based Access Control Security Systems
 Card-based access control security systems offer numerous benefits for businesses. They enhance security by allowing you to restrict door access to sensitive areas and monitor entry activity, reducing the risk of unauthorized entry by requiring user identification tied to the level of access. These systems also enable you to assign different access levels to different employees and staff, allowing you to manage building entry permissions & visitor credentials more efficiently.
Card-based access control security systems offer numerous benefits for businesses. They enhance security by allowing you to restrict door access to sensitive areas and monitor entry activity, reducing the risk of unauthorized entry by requiring user identification tied to the level of access. These systems also enable you to assign different access levels to different employees and staff, allowing you to manage building entry permissions & visitor credentials more efficiently.
Card-based access control systems help reduce administration costs by eliminating the need for traditional locks, keys, lock replacements and rekeying of door locks. Access to doors can also be controlled remotely, so nobody has to be physically present at a building to let someone in that has been locked out. They are easily scalable, making them ideal for businesses that expect to grow or change over time. Additionally, access control software can generate detailed audit trail reports on entry activity, helping you identify security breaches and improve overall security.
Choosing the Right Key Fob Access Control System for Your Business
 When selecting a key fob access control system, it's essential to consider factors such as security requirements, system compatibility, scalability, and cost. Determine the number of doors you want to control and the level of security you need before choosing an access system that will meet your specific requirements. Ensure the key fob access control system you select is compatible with your existing security infrastructure and can grow and adapt to your business's changing needs. Finally, consider both the upfront and ongoing costs of the door access control system, including hardware, software, and maintenance.
When selecting a key fob access control system, it's essential to consider factors such as security requirements, system compatibility, scalability, and cost. Determine the number of doors you want to control and the level of security you need before choosing an access system that will meet your specific requirements. Ensure the key fob access control system you select is compatible with your existing security infrastructure and can grow and adapt to your business's changing needs. Finally, consider both the upfront and ongoing costs of the door access control system, including hardware, software, and maintenance.

